Summary of the Apple T2 chip
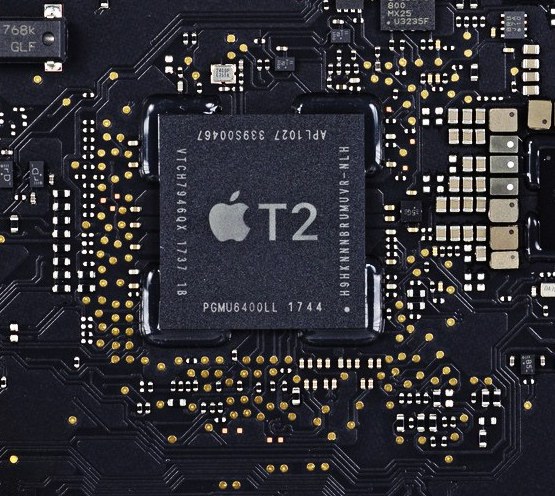
This is a summary of the Apple T2 chip shipping in lots of the new Mac models. It affects the boot process, disk encryption, TouchID and other areas, and is the main reason “imaging is dead”, so is an important topic.
There are some great write-ups on the T2 chip, like here: https://arstechnica.com/gadgets/2018/02/imac-pro-review-not-a-consumer-machine-but-not-quite-perfect-for-pros-either/3/ and of course from Apple: https://www.apple.com/mac/docs/Apple_T2_Security_Chip_Overview.pdf. For those of you that are short on time, this is a brief summary of the new chip and how it might affect you.
Please note, most of the details are our own notes / snippets from the Apple PDF linked above. The details are just paraphrased for quicker digestion!
History
This new chip first appeared in the iMac Pro and meant the death of imaging. We suspected the chip would spread to other models of Macs, removing the ability to boot to external media and make imaging impossible (at least without a big faff). Apple recently announced the new 15-inch MacBook Pro with a T2 chip, and this week, the MacBook Air and Mac mini have been added to the lineup.
Very, very brief summary
If you just want to know the changes that might impact you as a MacAdmin, here’s the very very brief summary:
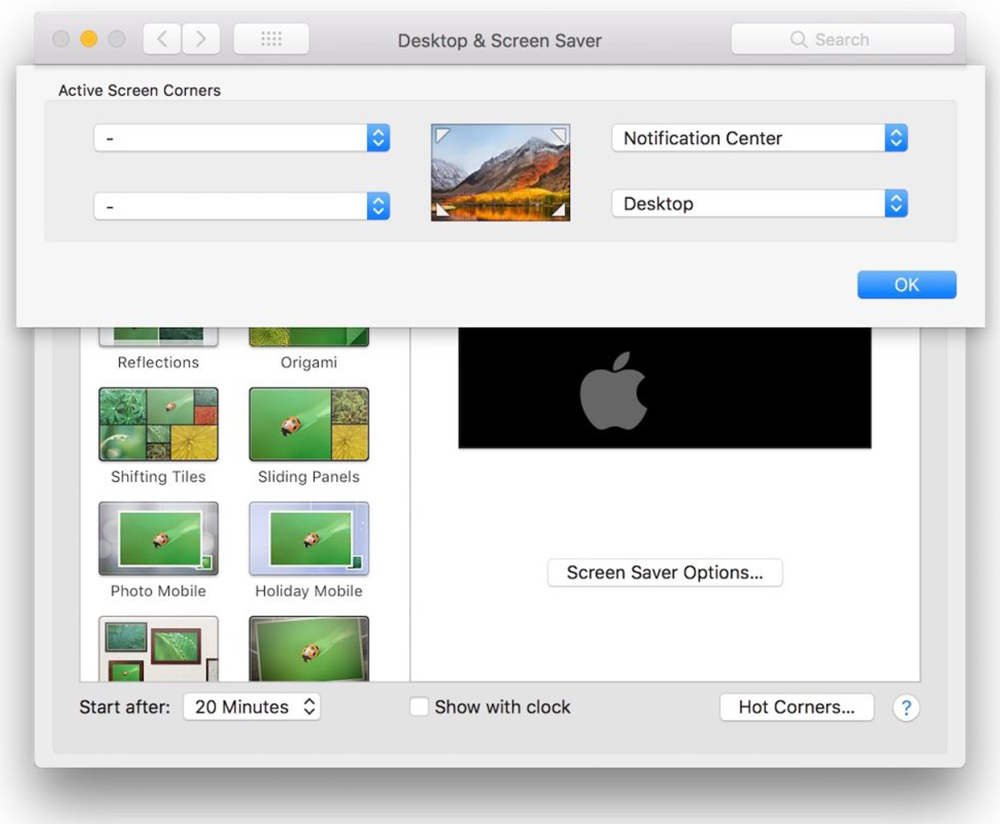
- It has a new feature called Secure Boot, which digitally signs the OS, but also ties it to the T2 chip in the Mac. This means if the OS is tampered with, or the disk is removed, it won’t boot up. So no more imaging!!
- The Mac won’t (by default) allow booting to external media
- The boot disk is always encrypted. “Enabling” FileVault just lets the user unlock the disk. This means that the encryption process appears to be instant (which is cool)
- The disk encryption is also tied to the T2 chip, so the disk will be unreadable if it’s removed and connected to another Mac (if that’s even possible!)
- Like the iPhone, exponentially increasing cool-off periods are added between incorrect login attempts. After the maximum is reached (although it is quite high), the T2 chip will no longer allow the disk to be decrypted.
- Oh, and the mic has a hardware disconnect when the lid is closed on MacBooks (I’m guessing there’s been some malicious eavesdropping software out there!)
- A bit more technical detail
If you’re interested in some of the more technical details, here they are:
General info
- The T2 chip integrates several controllers found in other Mac systems, including the system management controller, image signal processor, audio controller, and SSD controller
- It includes a Secure Enclave, which is a coprocessor, built solely to provide dedicated security functions
- It is FIPS 140-2 compliant
- It holds the cryptographic keys / information for secure boot, Touch ID and FileVault, amongst other things.
FileVault specifics
- It has a dedicated AES hardware engine included in the T2 chip, making encryption / decryption operations much, much faster
- The dedicated AES crypto engine is built into the DMA path between the flash storage and main system memory
- FileVault is using the AES-XTS cipher
- The AES engine makes available only the results of encryption or decryption operations it performs. The UIDs and GIDs aren’t available to debugging interfaces
- All APFS volumes are created with a volume key by default
- If FileVault isn’t enabled on a Mac with the T2 chip during the initial Setup Assistant process, the volume is still encrypted, but the volume key is protected only by the hardware UID in the Secure Enclave
- If FileVault is enabled later, the process is immediate since the data was already encrypted
- The volume is then protected by a combination of the user password with the hardware UID of the T2 chip
- If internal storage media are physically moved from one device to another, the files they contain are inaccessible. This protects the system from a brute-force attack directly against storage media removed from Mac
- On Mac systems with the T2 chip, all FileVault key handling occurs in the Secure Enclave; encryption keys are never directly exposed to the (Intel) application processor
- The Mac unique ID (UID) and a device group ID (GID) are AES 256-bit keys fused (UID) or compiled (GID) into the Secure Enclave during manufacturing. No software or firmware can read the keys directly
- Encryption of external media doesn’t utilise the security capabilities of the Apple T2 Security Chip, and its encryption is performed in the same manner as Mac computers without the T2 chip
- To prevent brute-force attacks, when Mac boots, no more than 30 password attempts are allowed at the Login Window or via Target Disk Mode, and escalating time delays are imposed after incorrect attempts. The delays are enforced by the Secure Enclave coprocessor on the T2 chip. If the Mac is restarted during a timed delay, the delay is still enforced, with the timer starting over for the current period
- If the 30 attempts are exhausted, 10 more attempts are available after booting into macOS Recovery. And if those are also exhausted, then 30 more attempts are available for each enabled FileVault recovery mechanism (iCloud recovery, FileVault recovery key, and institutional key), for a maximum of 90 possible attempts. Once those attempts are exhausted, the Secure Enclave will no longer process any requests to decrypt the volume or verify the password
Secure Boot
- Each step of the startup process contains components that are cryptographically signed by Apple to verify integrity
- The boot process proceeds only after verifying the integrity of the software at every step, which creates a chain of trust rooted in hardware
- At boot, the first code to be executed is the Boot ROM. This is read-only, is laid down during chip fabrication and is audited for vulnerabilities and implicitly trusted
- The Boot ROM code contains the Apple Root CA public key, which is used to verify that the bootloader is signed by Apple’s private key before allowing it to load
- You can still use Recovery mode, Diagnostics mode, and Internet Recovery mode, but these modes only proceed after successful verification of the integrity of the critical system files used for the boot mode, whether stored locally or downloaded from the Internet
- For anyone using Bootcamp, the latest version of Windows is also subject to Secure Boot
- If there’s an issue, the Mac will boot into macOS Recovery. which then launches the Boot Recovery Assistant application
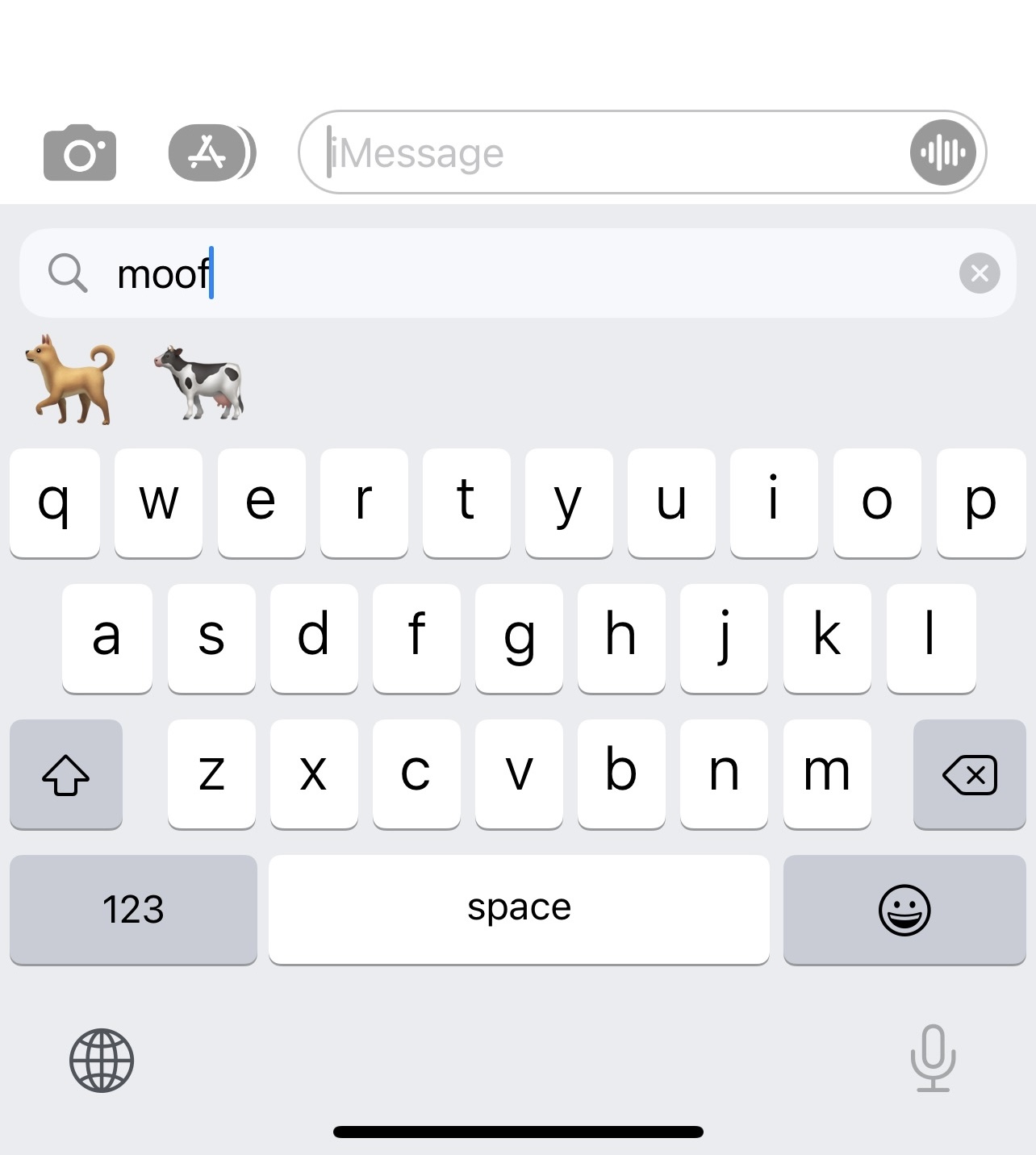
- You can change the Secure Boot modes using Startup Security Utility from the Recovery partition
- When Startup Security Utility is first opened, it prompts the user to enter an administrator password from the primary macOS installation associated with
the currently booted macOS Recovery - If no administrator exists, one must be created before the policy can be changed
TouchID
- TouchID can unlock the Mac, authorise purchases from the iTunes Store, App Store, and Apple Books, as well as with Apple Pay
- It doesn’t store any fingerprint images, instead it relies only on a mathematical representation of the fingerprint
- This representation is encrypted, stored on the device, and protected with a key available only to the Secure Enclave
- It’s never sent to or stored on Apple’s servers
If you want a deeper explanation, I’d recommend having a read of the Apple PDF: https://www.apple.com/mac/docs/Apple_T2_Security_Chip_Overview.pdf
Our conclusion… Apple have achieved a great feat, to increase security, without impacting the user experience or making the device less useable. For those of you familiar with the seesaw analogy of security, this is like bending the laws of physics, so well done Apple ????????.